Your Trusted Partner for Vulnerability Assessment & Penetration Testing (VAPT)
VAPT Services in Dubai – Protect Your Business from Cyber Attacks Today
Certified Experts | Fast Reports | UAE Compliance Ready


“Serving clients across Dubai, Abu Dhabi, and the UAE”
Grabanoid delivers professional VAPT services in Dubai to help organizations identify security vulnerabilities, validate real-world attack scenarios through penetration testing, and strengthen their cybersecurity posture. Our vulnerability assessment and penetration testing services cover web applications, mobile applications, APIs, network infrastructure, and OT/IIoT environments across UAE and GCC.
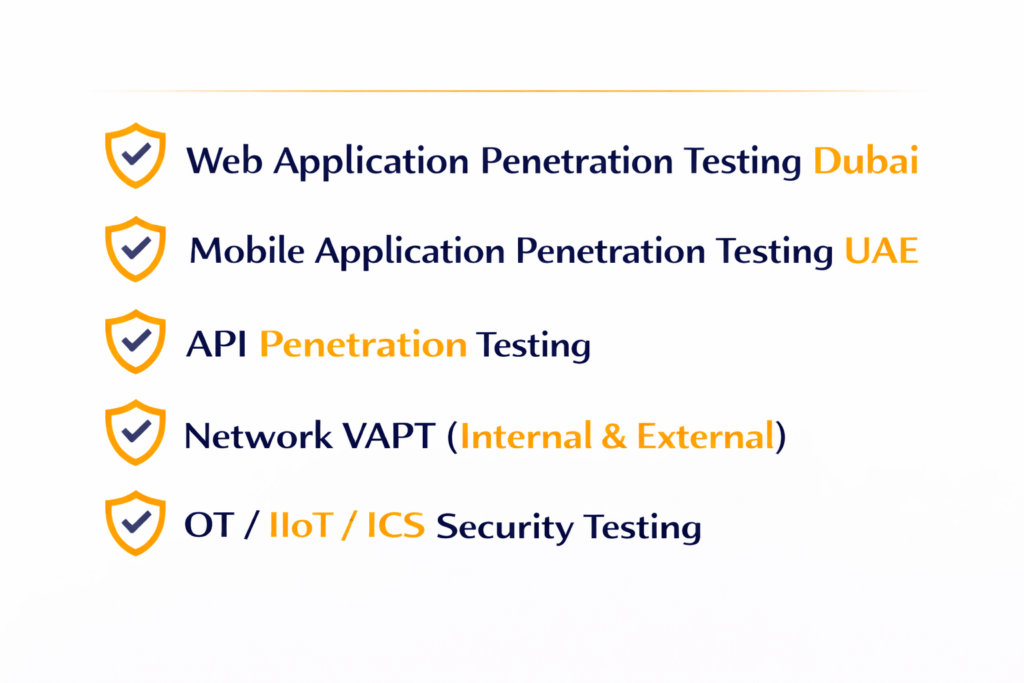

OUR SERVICES
VAPT That Finds Real Risk — Not Just Scan Results
Identify exploitable weaknesses across your applications, infrastructure, cloud, and APIs—then get a prioritized remediation roadmap you can actually implement.
WEB APP
Web Application Penetration Testing (Dubai)
OWASP Top 10 testing to uncover authentication flaws, access control issues,
data exposure risks, and business logic vulnerabilities.
MOBILE APP
Mobile Application Penetration Testing (UAE)
Security testing for Android and iOS apps, including secure storage,
API communication, runtime behavior, and data leakage.
NETWORK
Network Penetration Testing (Internal & External).
Identify exposed services, weak credentials, misconfigurations,
and lateral movement risks across your infrastructure.
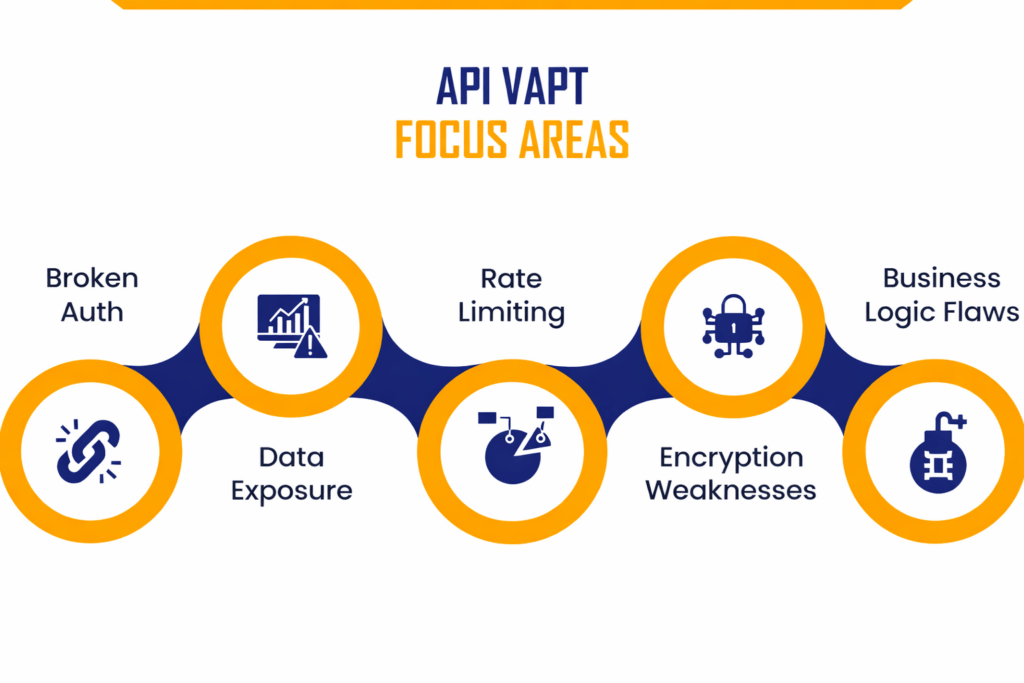
API
API Penetration Testing
- Broken authentication & authorization
- Excessive data exposure
- Rate limiting & abuse testing
OT / IIoT
OT / IIoT / ICS VAPT
- Industrial systems security
- SCADA & ICS risk validation
- List Item #3Segmentation & protocol testing

Our Solution
- Automated and manual vulnerability identification
- Real-world attack simulation by security experts
- Identification of exploitable security weaknesses
- Risk-based vulnerability prioritization
- Validation of vulnerabilities through controlled exploitation
- Clear remediation guidance and recommendations
What You Receive from Grabanoid VAPT
- Executive summary for leadership (risk + business impact)
- Technical report with CVSS scoring & proof-of-concept evidence
- Prioritized remediation plan (quick wins + strategic fixes)
- List ItemRetest validation (optional) to confirm closure
- List Item Recommendations aligned to best practices (OWASP / CIS where applicable)
Why Choose Grabanoid for VAPT in Dubai/UAE
- Manual testing to reduce false positives
- Business-impact focused findings
- Audit-ready reporting (ISO 27001 support)
- Confidential, NDA-ready engagements
- Dubai-based delivery & regional expertise

FAQ
Everything you need to know about VAPT services in Dubai
A:Vulnerability assessment identifies weaknesses, while penetration testing validates exploitability and real business impact.
A: Typically from a few days to several weeks depending on scope and complexity.
A: Yes, our reports support security governance and audit requirements.
A: Yes, re-testing confirms remediation effectiveness.

